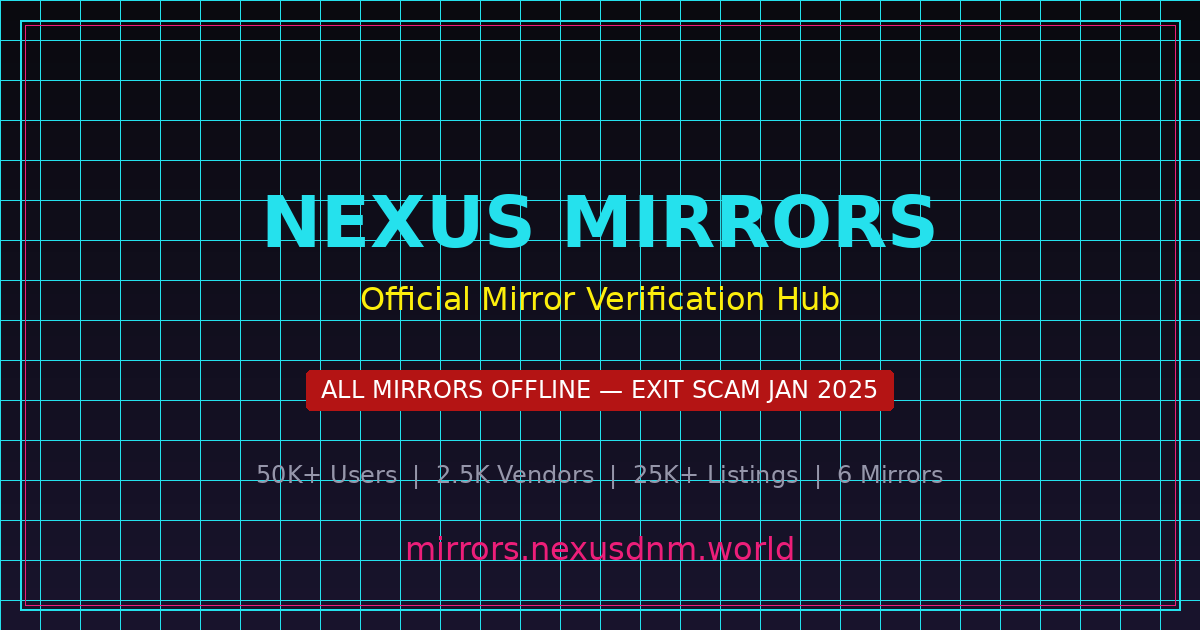
Critical Security Warning: All Nexus Market Mirrors Are Offline
Since the Nexus Market exit scam on January 18, 2025, every legitimate mirror link has been permanently taken offline. However, phishing operators have been quick to exploit the situation by creating fraudulent websites that impersonate this darknet marketplace. These phishing mirrors are designed to look identical to the original platform interface, complete with copied CSS styles, login forms, and even fake product listings. Their sole purpose is to steal login credentials and cryptocurrency from unsuspecting users who believe they are accessing a working Nexus Market URL.
Phishing attacks targeting darknet market users have become increasingly sophisticated over the past several years. Modern phishing mirrors often register onion addresses that visually resemble the original market URL, using character substitution techniques to create addresses that appear legitimate at first glance. Some phishing operators go further by deploying man-in-the-middle proxies that relay traffic between the victim and a legitimate service, capturing credentials and session tokens in real time. In the case of Nexus Market, any site claiming to be a functioning mirror is definitively a scam because the underlying marketplace infrastructure no longer exists.
The financial impact of darknet market phishing is substantial. According to research from cybersecurity organizations like OWASP and government agencies such as CISA, phishing remains the most common attack vector for credential theft across all sectors of the internet. On the dark web, the consequences are amplified because victims have no legal recourse and transactions in cryptocurrency are irreversible. Understanding how to identify phishing mirrors is therefore a critical skill for anyone navigating the darknet.
Below is a checklist of red flags that indicate a Nexus Market mirror link is fraudulent. If you encounter any of these warning signs, close the site immediately and do not enter any credentials or send any cryptocurrency.
×
The site claims to be a working Nexus Market mirror after January 18, 2025 — all legitimate mirrors are permanently offline following the exit scam.
×
The onion address does not match any URL from the last PGP-signed mirror list published by the Nexus Market administrators before the shutdown.
×
The site asks you to deposit cryptocurrency before allowing access to your account or displaying your order history.
×
Your personalized anti-phishing phrase is missing, incorrect, or never displayed after you log into the account dashboard.
×
The PGP signature on the mirror list cannot be verified against the known Nexus Market public key, or no signed mirror list is provided at all.
×
The site contains unusual spelling errors, broken page layouts, missing images, or other visual inconsistencies not present on the original Nexus Market.
×
The login page loads unusually slowly, which may indicate a man-in-the-middle proxy relaying your requests through an intermediary server.
×
The site prompts you to disable JavaScript, install browser extensions, or download files — actions that could compromise your system security or anonymity.
×
The CAPTCHA system on the login page differs from the one used by the original Nexus Market, or no CAPTCHA is presented at all.
×
Forum posts or messages promoting the mirror link come from newly created accounts with no established reputation or post history.
For a detailed security guide covering these topics, visit our Security Verification Guide. That page includes step-by-step instructions for PGP verification, Tor Browser configuration best practices, and additional resources for identifying fraudulent darknet market mirrors. Protecting yourself from phishing requires a combination of technical verification and cautious behavior — never trust a Nexus Market mirror link without completing the full verification process outlined above.